If you’re building a connected product, someone on your team has probably raised the question: do we need secure boot? The answer depends on what you’re building, where it’s deployed, and what’s at stake if someone tampers with the firmware running on your device.
This guide breaks down secure boot for product developers and engineering leads, not security researchers, so you can make an informed decision early in your product development cycle. For a broader look at how secure boot fits into your product’s overall security architecture, see our guide to embedded product security.
What Is Secure Boot?
Secure boot is a mechanism that ensures only authenticated, unmodified firmware runs on your device. Every time the device powers on, it verifies that the software hasn’t been tampered with before executing it.
The core concept is the chain of trust:
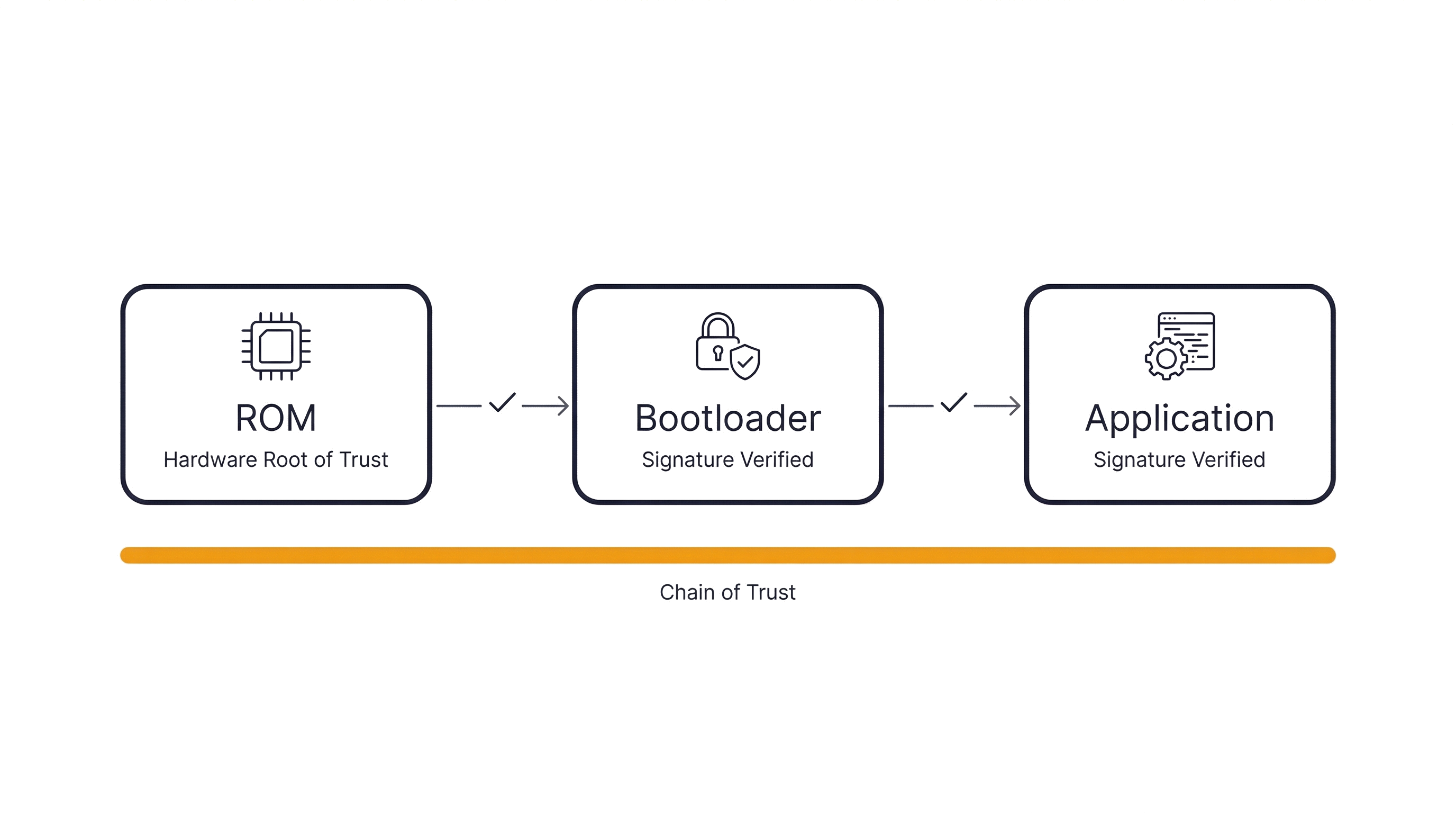
- Hardware root of trust. An immutable piece of code burned into the chip’s ROM starts execution. Because it can’t be modified, it’s inherently trusted.
- Bootloader verification. The ROM code cryptographically verifies the bootloader’s digital signature before handing off control.
- Application verification. The bootloader then verifies the main application firmware the same way.
If any link in this chain fails verification, because the firmware was modified, corrupted, or replaced, the device refuses to boot that code. Trust flows from hardware all the way up to your application.
Why Product Developers Should Care
Secure boot isn’t just a checkbox for security audits. It addresses real risks that product teams encounter once devices ship:
- Firmware tampering in the field. Devices deployed in accessible locations (utility meters, EV chargers, industrial controllers) can be physically accessed. Without secure boot, an attacker can flash malicious firmware with nothing more than a debug probe.
- Counterfeit protection. If your product is successful, clones appear. Secure boot makes it significantly harder to copy your firmware onto unauthorized hardware.
- Safe OTA updates. Over-the-air updates are essential for connected products, but a compromised update pipeline can brick entire fleets. Secure boot ensures only properly signed updates execute.
- Regulatory exposure. Standards like IEC 62443 for industrial systems, FDA cybersecurity guidance for medical devices, and UNECE WP.29 for automotive all increasingly require firmware integrity mechanisms.
- IP protection. Your firmware represents years of R&D. Secure boot, combined with encrypted storage, makes extraction and reverse engineering substantially harder.
How Secure Boot Works in Embedded Systems
The core principles are the same as UEFI Secure Boot on PCs, but the implementation looks very different. There’s no standardized firmware interface, no key enrollment UI, and far tighter resource constraints. Everything runs on bare-metal microcontrollers, often with just kilobytes of RAM.
The MCU-Level Implementation
At the hardware level, modern MCUs from vendors like STMicroelectronics, NXP, and Microchip include dedicated security features that make secure boot practical:
- One-time programmable (OTP) fuses store the root public key hash. Once burned, this value can never be changed. It becomes the hardware root of trust.
- Crypto accelerators handle signature verification efficiently. Without hardware acceleration, verifying an RSA or ECDSA signature on a Cortex-M4 could add seconds to boot time. With it, verification completes in milliseconds.
- Secure storage regions protect keys and critical data from read-out, even through debug interfaces.
What Happens When Verification Fails
A well-designed secure boot implementation needs a clear failure policy. Common approaches include:
- Halt. The device refuses to boot. Simple and secure, but a bad update could leave a device permanently non-functional without physical intervention.
- Fallback. The device reverts to a known-good, previously verified firmware image. This is the approach most production systems use because it provides resilience against failed updates.
- Recovery mode. The device enters a minimal, signed recovery environment that can accept a new, properly signed update.
The right choice depends on whether your devices are physically accessible for service, or whether they need to recover autonomously in the field.
When Your Product Needs Secure Boot
Not every embedded product requires secure boot. A simple sensor that reports temperature readings over a local bus has a different threat model than a networked medical device. Here’s a practical decision framework.
You almost certainly need it if:
- Your device receives OTA firmware updates over a network
- It’s deployed in physically accessible or unattended locations
- It handles sensitive data (personal, financial, health, or safety-critical)
- Your target market has regulatory requirements (medical, automotive, industrial, energy)
- Multiple parties in your supply chain touch the firmware before it reaches end users
You can probably defer it if:
- The device is a simple peripheral without network connectivity
- Firmware is only programmed at the factory and never updated
- The device operates in a physically secure, controlled environment
- There’s no sensitive data and no safety implications from modified firmware
Even in the “defer” cases, consider that product requirements evolve. A device designed without networking today may need OTA updates in the next hardware revision.
What It Costs You
Secure boot is not free. Being honest about the tradeoffs helps you plan and budget appropriately:
- Development complexity. Implementing a secure bootloader takes focused engineering effort. Expect it to add meaningful time to your firmware development schedule, more if your team hasn’t done it before.
- Key management. You need a strategy for generating, storing, and rotating cryptographic keys. This is an operational process, not just a technical one. Who holds the signing keys? How are they backed up? What happens if a key is compromised?
- Hardware requirements. You’ll need an MCU with appropriate security features: crypto acceleration, OTP fuses, and secure storage. This can influence chip selection and BOM cost.
- Development workflow. Developers can’t just flash unsigned firmware during debugging. You’ll need to integrate code signing into your build pipeline and establish a workflow for development builds versus production builds.
- Boot time. Signature verification adds time to the boot sequence, though hardware crypto acceleration keeps this to tens of milliseconds on most modern MCUs.
Getting Started
If you’ve decided secure boot belongs in your product, here’s what to evaluate early, before you’re deep into firmware development:
- MCU selection. Choose a microcontroller with hardware security features appropriate for your needs. Look for hardware crypto engines, OTP memory for key storage, and vendor-provided secure boot examples or reference implementations.
- Key provisioning strategy. Decide how cryptographic keys will be generated, who controls them, and how they’ll be injected into devices during manufacturing. This touches your supply chain and factory processes.
- Secure boot and OTA interaction. Your secure boot design and your OTA update design are tightly coupled. The update mechanism needs to deliver signed images, and the bootloader needs to verify them. Design these together, not separately.
- Failure and recovery policy. Define what happens when verification fails. Consider your deployment environment: can a technician physically access the device, or does it need to self-recover?
Getting the architecture right early saves significant rework later. If you’re evaluating these decisions for an upcoming product, our embedded security services can help you move faster with confidence.